The Human Anchor: The Blind Spot in Tracking Freight Fraud

In June 2025, a commercial truck hauling U.S. mail for a company called Hope Trans LLC was involved in a horrific crash on I-20 near Terrell, Texas. Five people were killed.
In the aftermath, it was revealed that the principals behind Hope Trans had operated multiple prior trucking companies that had been shut down due to severe safety issues. Yet, they were still on the road, still booking freight, and still entrusted with federal mail.
If you want to stop tendering freight to dangerous chameleon carriers, you can't treat every new DOT number as a blank slate. You have to look for the hidden connections.
Here is exactly how AlphaLoop mapped the network behind that crash and the terrifying blind spot that even advanced investigations often miss.
Step 1: Tracking the Metal from Bee Zone
Long before Hope Trans LLC made headlines, a different carrier frequently popped up on load boards: Bee Zone Logistics (USDOT 3191514).
On the surface, Bee Zone looked perfectly clean. They had an active authority, a clean safety record, and no red flags on public FMCSA portals. But when we loaded Bee Zone's inspection data into the AlphaLoop network graph, we decided to track their physical equipment (see our previous post on Tracing the Metal for more on this process).
We asked the graph: Has Bee Zone Logistics ever shared a truck VIN with any other company?
The graph immediately lit up.
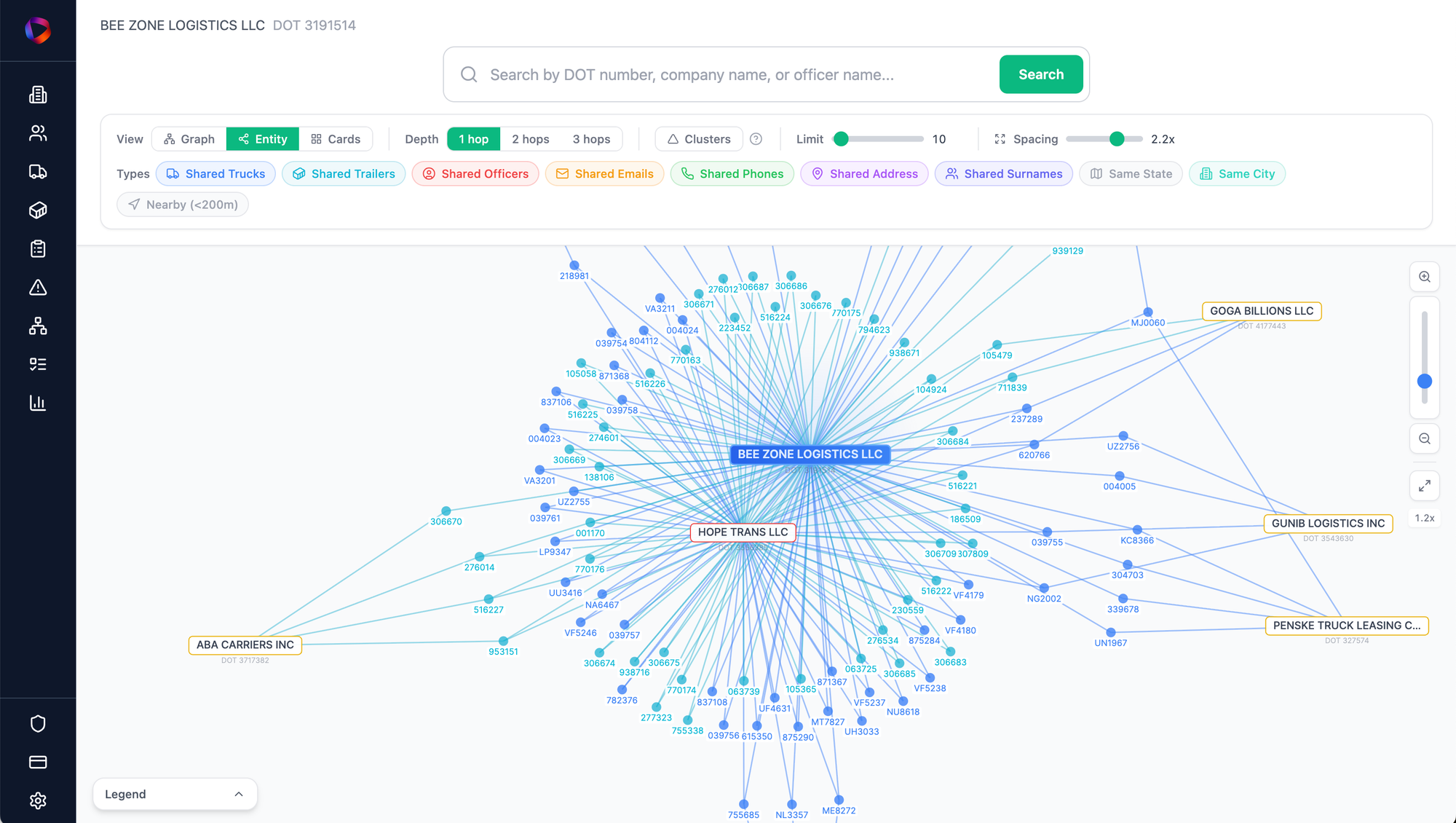
By tracking the metal, we found that trucks originally registered to the clean-looking Bee Zone Logistics were migrating directly into the fleet of Hope Trans LLC. Bee Zone was effectively acting as an equipment pipeline for a highly dangerous, obscured operation.
Step 2: The Blind Spot in Tracking Equipment
Tracking the metal caught Hope Trans. But relying solely on equipment data creates a massive blind spot.
Sophisticated fraud networks know that investigators and brokers track physical trucks. To protect their operations, they will often "silo" their assets. They make sure the trucks used in Scheme A never touch the companies running Scheme B, creating a physical firewall in the data.
If we had stopped our investigation after mapping Bee Zone's shared trucks, we would have missed the rest of the operation. There were other carriers out there that should have been caught, but weren't, simply because they intentionally never shared a single piece of equipment with Bee Zone.
To leapfrog over those physical firewalls, you have to stop tracking the metal and start tracking the people.
Step 3: The Human Anchor
We went back to Bee Zone Logistics and bypassed their equipment data entirely. Instead, we looked at their corporate filings to see who was actually pulling the strings.
That is where we found a single name: Patina Magomedova.
In an isolated spreadsheet, an officer’s name is just a string of text. But on a network graph, a person becomes a central node. We ran a new query through the entirety of the FMCSA database: What other companies is Patina Magomedova connected to?
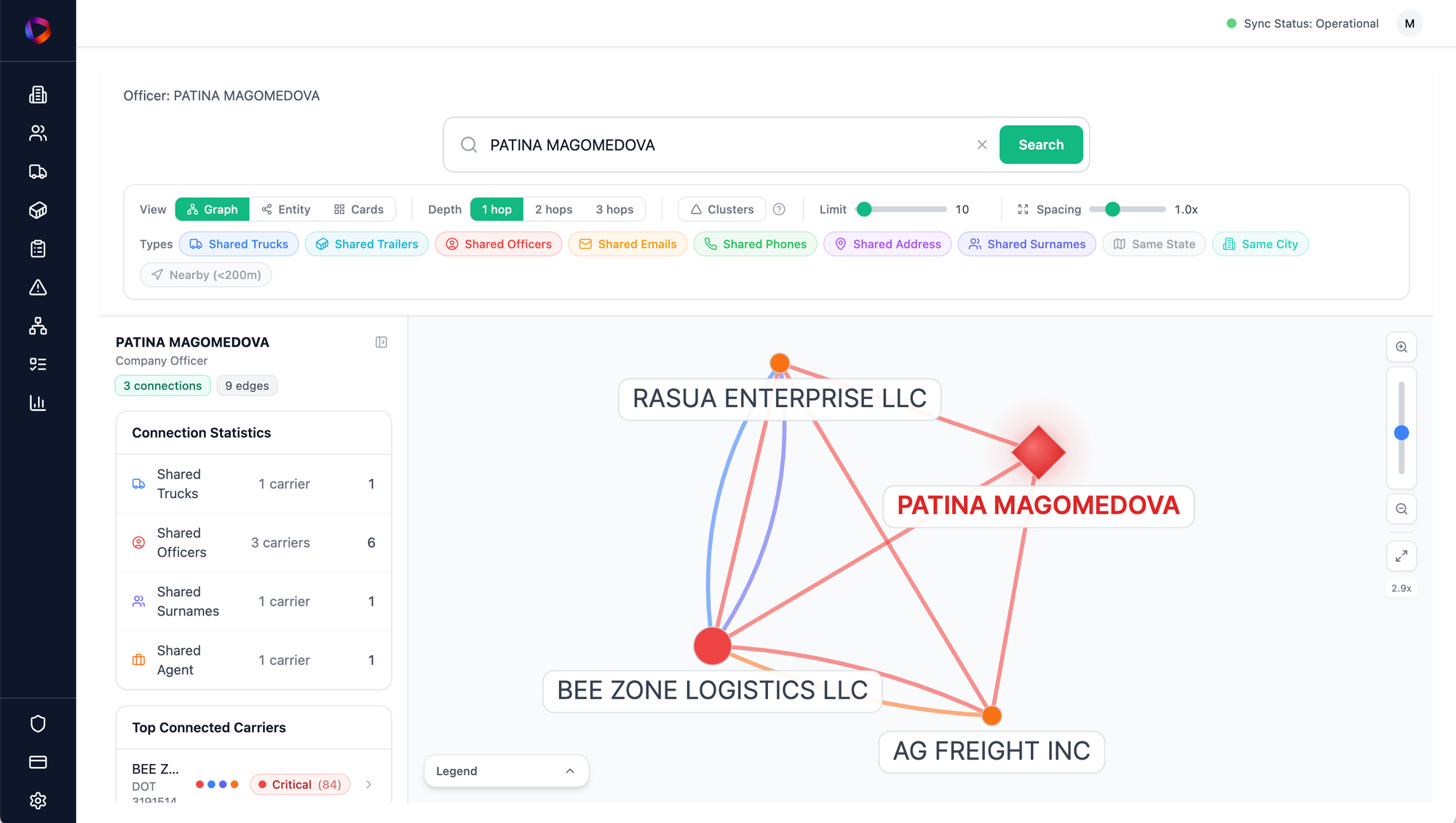
The results exposed the silos.
The AlphaLoop graph revealed that Patina was the exact same registered officer for completely separate companies, including AG Freight Inc (USDOT 4110997) and Rasua Enterprise LLC (USDOT 3561352).
These entities were physically isolated from Bee Zone. They had different DOT numbers, different trucks, and completely different operational footprints. If you only tracked the metal, AG Freight and Rasua Enterprise looked like entirely unrelated businesses.
But behind the digital curtain, they were anchored by the exact same human infrastructure.
The Takeaway: Vet the Network, Not the Number
The Terrell, Texas crash wasn't an unavoidable accident committed by a standalone company. It was the tragic result of an obscured network that had been shifting assets and liabilities for years.
If your vetting process stops at the public FMCSA portals, you are flying blind. And if you rely solely on tracking physical trucks, you are still vulnerable to the networks that know how to hide their fleets.
To truly understand the risk of a carrier, you have to map the entire operation. You have to trace the shared vehicles, map the human officers, and let the network graph reveal the hidden operations that a simple background check could never catch.
