Why Traditional Carrier Vetting is Failing (And How to Actually Catch a Chameleon)
Public FMCSA data can't catch a chameleon carrier. Learn how mapping historical data and social listening exposes hidden freight fraud before it strikes.

The freight industry is hemorrhaging billions to industrialized fraud. From double-brokering cartels to chameleon carriers dodging out-of-service orders, bad actors have figured out how to weaponize the very systems designed to keep the supply chain safe.
Yet, when it comes to carrier vetting, much of the industry is still relying on the equivalent of checking a driver’s license and hoping it’s not fake.
If you are only looking at public-facing FMCSA portals like SAFER to vet a carrier, you are only seeing a carefully curated snapshot of the present. You aren't seeing the history, the hidden connections, or the shell games happening just beneath the surface.
Here is why traditional vetting is failing, and how modern data architecture is finally turning the tables.
The Problem: Snapshots Don’t Catch Shell Companies
When a carrier is shut down for severe safety violations or racketeering, the physical trucks don't disappear. Instead, the operators simply spin up a new shell company, apply for a fresh DOT and MC number, and flip the switch. This is the "chameleon carrier" playbook.
Public databases are built to show you a carrier's active operating status. They are not built to show you that the exact same truck VINs, officers, and phone numbers were registered to three other defunct companies over the last 18 months. By the time a new shell company shows a bad safety rating on SAFER, the damage is already done and the fraud ring has moved on to their next iteration.
To catch these networks, you have to stop looking at carriers in isolation.
The Solution: Mapping the Invisible Web
If you have ever watched a detective movie, you know what a network graph is.
Think of the classic corkboard covered in pushpins and red string. The investigator pins up a photo of a suspect, a specific street address, and a burner phone number. Then, they use red string to connect the pins, visually proving that two seemingly unrelated suspects both called the same burner phone from the same address.
A network graph is just a digital, massively scaled-up version of that corkboard.
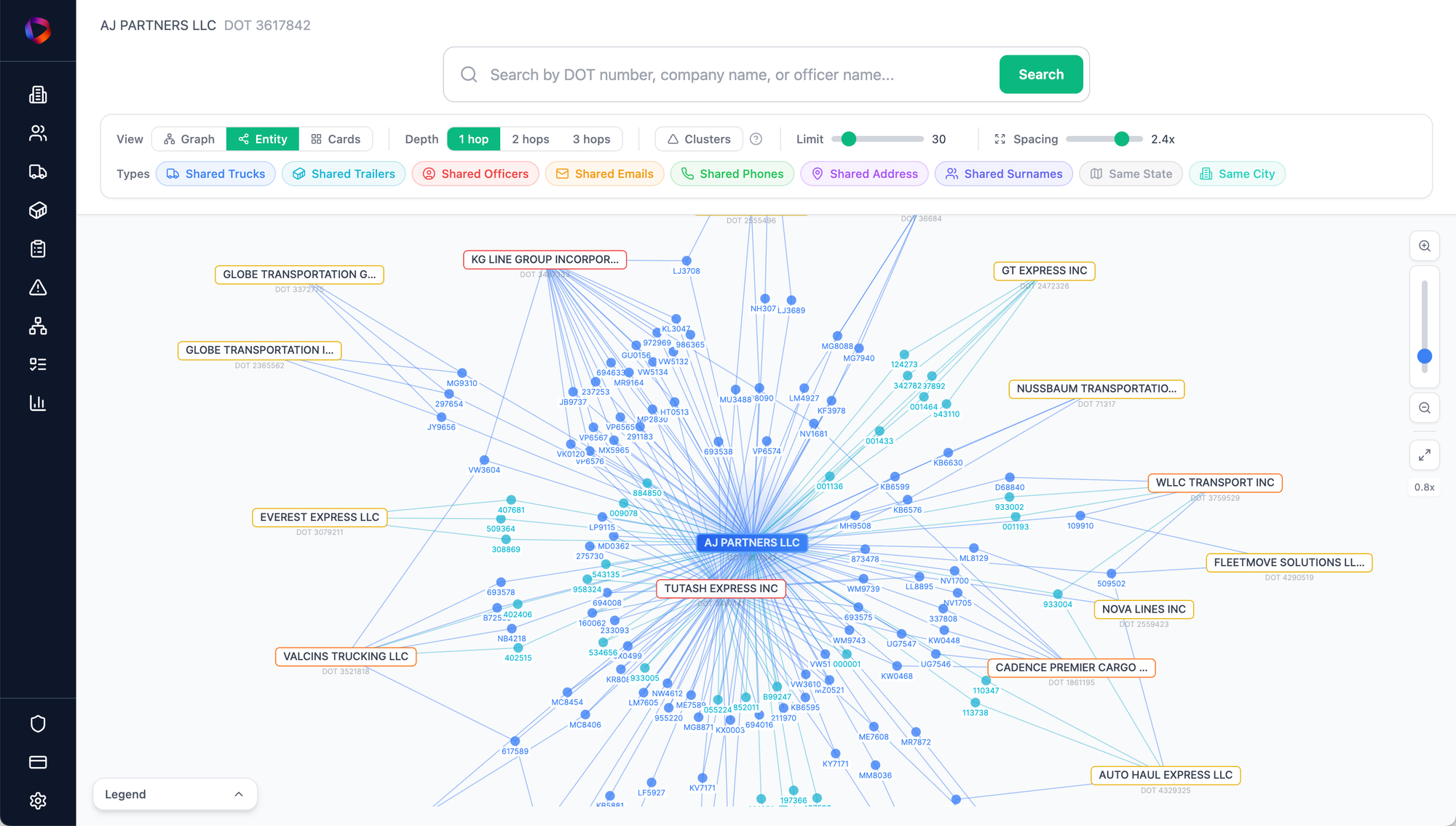
Instead of pushpins, we have "nodes." A node can be anything: a specific DOT number, an officer's name, a truck's VIN, or a registered Gmail address. Instead of red string, the software automatically draws lines between any nodes that share a connection in the raw historical data.
When you load the entirety of the FMCSA database onto this digital corkboard, the invisible ties become impossible to hide. We aren't just looking at isolated company names; we are mapping the underlying infrastructure:
- The People: Shared officers and registered agents.
- The Contact Info: Burner phone numbers and shared Gmail addresses.
- The Assets: Trucks, trailers, and individual VINs.
- The Geography: Cities, states, and the exact same residential apartment numbers being used for dozens of "headquarters."
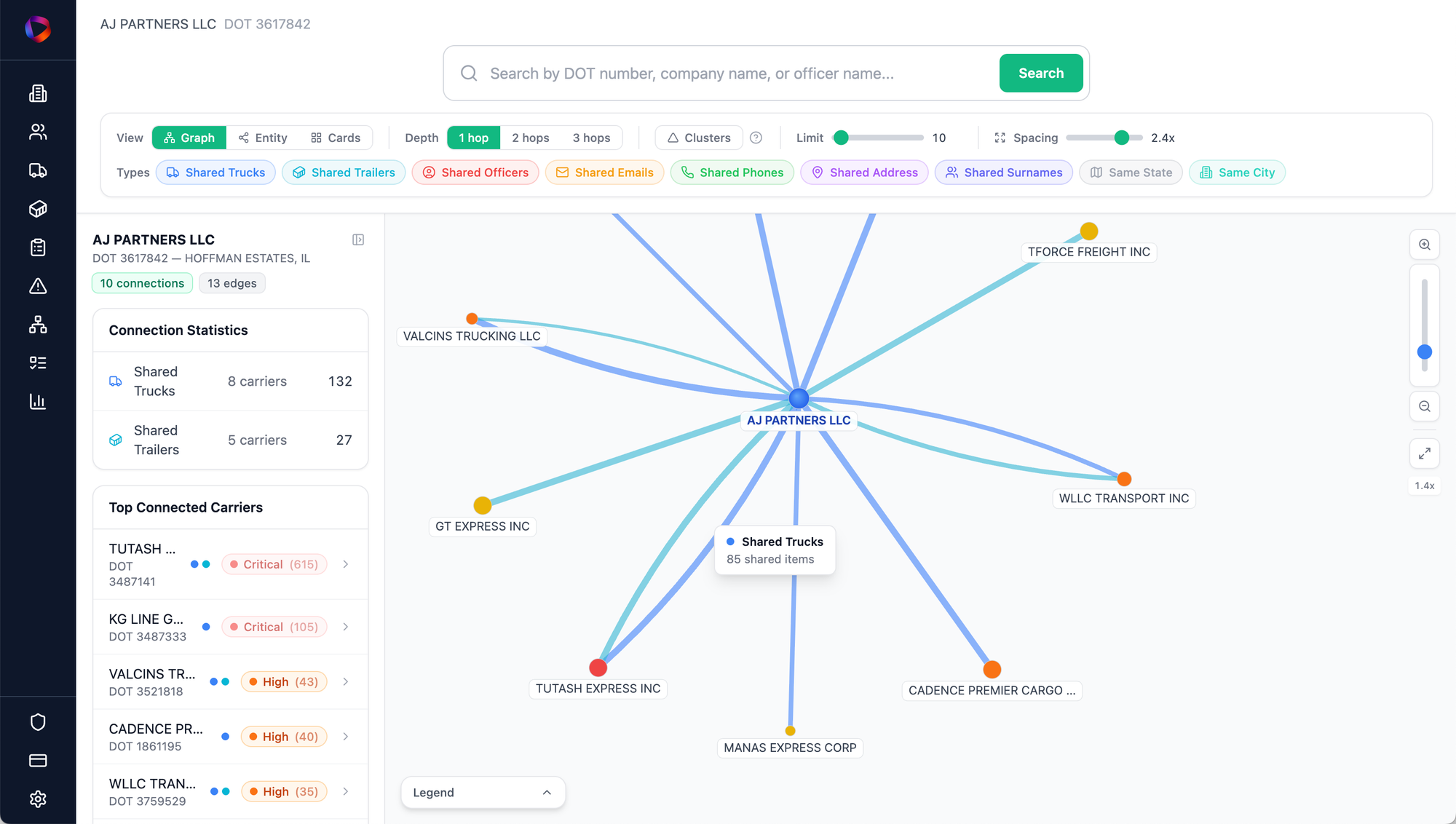
When you map these data points, the patterns emerge immediately. By grouping these connected nodes tightly together, massive, multi-layered fraud rings become instantly recognizable. What looks like 50 independent carriers on a spreadsheet is visually exposed as a single, coordinated spherical cluster of operations.
Layering in Risk Signals
Connecting the raw FMCSA data is only half the battle. To catch bad actors before the federal data officially catches up to them, we layer in Risk Signals.
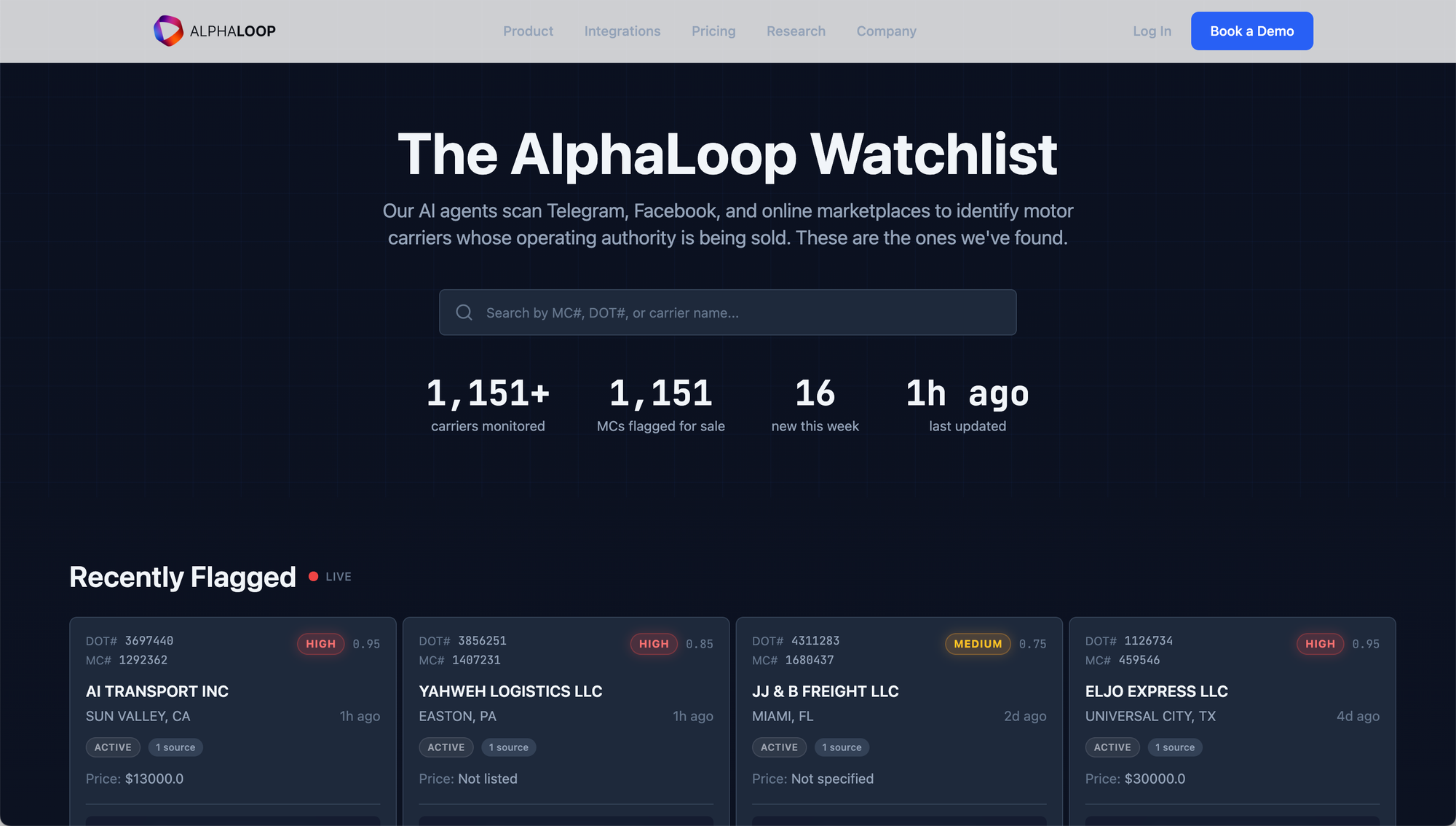
This involves dedicated social listening—crawling the web for mentions across trucking forums, social networks, and court filings. Often, the earliest indicator of a distressed or fraudulent carrier isn't a federal out-of-service order; it's a Reddit thread from an owner-operator who hasn't been paid in 60 days, or a furious Facebook post from a driver warning others about a specific dispatcher's phone number.
When you combine a sprawling FMCSA data cluster with these real-time, web-scraped risk signals, you have a bulletproof vetting mechanism. You aren't just waiting for an official out-of-service order; you are catching the early warning signs before the damage is done.
Up Next: Tearing Down a Cartel
Understanding the methodology is just the start. Over the next few weeks, we are going to use this technology to tear down real-world examples of freight fraud.
In our next post, we will walk step-by-step through a specific chameleon carrier network, showing exactly how dozens of trucks seamlessly shifted across multiple shell companies to dodge regulators—and how the data eventually caught them.